In-Depth
Trusted Storage for Enterprise-class Hard Disk Drives, Part 1 of 2
Encryption directly on the storage device provides the simplest and most effective means to obtain a trusted storage system.
By Michael Willett
Large corporations and government organizations, as well as medium and even small companies, have increasingly recognized the need to protect sensitive data on storage devices. To achieve trusted storage, data encryption, including full-disk encryption (FDE), requires implementation decisions and a strategy to avoid system problems, including performance degradation. Working in an industry standards group, storage manufacturers have developed a standards-based approach to prevent data theft in the enterprise. Before discussing the proposed solution, a review of the problem, including the need for encryption and the organization that developed a compelling response, is in order.
The Foundation for Security and Encryption
At the enterprise level, there are three compelling reasons to encrypt data at rest:
- Legislative compliance guidelines
- Threat of data loss
- Readability of discarded drives
According to research firm IDC's Dec. 2006 report, "Enterprise Security Survey: The Rise of the Insider Threat," large companies (those with more than 10,000 employees) perceive the internal security threat as greater than an external attack. Medium-size companies with 100 to 999 employees weigh in at about the same level, and smaller companies with fewer than 100 employees regard external threats as greater than internal ones. Since successful small, medium, or large companies grow, a scalable solution is part of the requirement for both internal and external security threats.
As part of its overall effort for enterprise-wide security, the Trusted Computing Group (TCG), an industry standards group focused on security, has created an open specification that enables FDE for hard disk drives. Also known as self-encrypting drives (SEDs), the encryption and key management processes used in these drives are defined in the specification. The process is hardware-based, scalable, and transparent to the user. With a self-encrypting drive, once it is installed in the system, data is automatically and continually encrypted. Without authentication to access the drive, that can occur if the system is lost or stolen, the hard drive locks and becomes useless. Unlike software encryption that typically reduces system performance, this hardware-based encryption does not impact performance and it is automatically implemented without user intervention.
Compelling Reasons for Encryption
More than 41 breach notification laws exist in the United States, and the number continues to grow. These laws stipulate that a company entrusted with confidential or sensitive information must provide a breach notification to users if data is lost or stolen. With FDE, no notification is required as long as it can be proven that the data was encrypted. This provides a strong case for automatic and continuous encryption.
The consequences of losing confidential data can be severe. Non-compliance with such laws can result in fines into the millions of dollars for the institution and its officers, and prison time as well as individual civil fines and additional litigation. According to the Ponemon Institute's November 2005 estimate, the average cost of a security beach is $14 million per incident.
Data protection is a global issue. For example, Japan has the Personal Information Protection Law that went into effect April 1, 2005. The United Kingdom Data Protection Act (DPA) of 1998 defines a legal basis for the handling of personal information. While interpretation can be an issue, technology improvements will play an increasingly important role to simplify and prevent the inadvertent disclosure of information.
Since the majority of U.S. states and the European Union have "safe harbor" provisions in their statutes for encryption, FDE is an alternative to costly reporting, remediation, and fines. Providing confidence in the effectiveness of FDE, the National Security Agency (NSA) has qualified at least one self-encrypting hard drive for protecting the information in computers used by U.S. government agencies and contractors for national security purposes. Obviously, data for non-government entities also can be protected by seamless and automatic FDE security.
Whether an organization is concerned with internal or external security threats, eventually every drive leaves the data center. The normal reasons for this occurrence can include maintenance, reconditioning, failure, or end-of-life. However, drives can also be lost in, or stolen from, a data center.
On a daily basis, some 50,000 drives are decommissioned from data centers. Regarding any of these drives as unusable or less of a threat could be a major mistake. IBM reports that 90 percent of drives returned because of a problem were still readable. On-drive encryption protects the data center under normal operation and when the storage unit leaves the data center for any reason. The industry-developed specifications for secure data storage solve the security issue both inside and outside the data center.
Disaster preparation is a hot topic for the data storage community that also provides further justification for FDE drives. This year's recent hurricane season and the reminder of Katrina's devastating effect on businesses as well as individuals, makes a strong case for FDE, especially to those who thought that the severely damaged drives would not yield their secrets. Consider that data was retrieved from the platters on the 400 MB, 2.5-inch drive from the Columbia shuttle disaster. As part of looting prevention during disasters, FDE should be considered an essential part of disaster preparedness for any business with sensitive data.
Encryption Prevents Data Theft
Encryption is clearly one answer to the data security problem. However, there are many points where encryption can be implemented in the data center, and protection can be software- or hardware-based.
First, consider the software versus hardware decision. In addition to the performance burden that software adds, the viruses and malware it attempts to prevent can often attack software-based schemes, making hardware-based encryption a better alternative to a software-based solution.
Where should the encryption be located? Encryption performed directly on the hard drive has several advantages over any upstream location in the data center. Data de-duplication and data compression are two areas that demonstrate the impact of location on system performance and efficiency.
Rather than have the same data stored in several locations, de-duplication tools work with plain text, storing it and pointing to that data whenever it is needed. These techniques free up a significant amount of storage space. However, the same data encrypted at different points in the data stream may be quite different in encrypted form. As a result, de-duplication cannot be performed with encrypted data.
Data compression is another area directly affected by encryption. Decompression techniques require redundancy in the message to compress data. Since encrypted data appears totally random, it has no built-in redundancy and cannot be compressed.
Encrypting too early in the data flow makes de-duplication and decompression algorithms ineffective. Premature encryption also impacts end-to-end integrity metrics. Within the data center, this means that one location is the obvious choice for performing encryption – at the drive itself. The advantages of encrypting directly on the drive are easily demonstrated with de-duplication and decompression but there are several other system advantages.
Perhaps an even greater system issue is complexity. Figure 1 shows a comparison of key management with encryption on the drive versus outside the drive. Four encryption keys are eliminated from the data center when the encryption is performed at the storage system with self-encrypting drives.
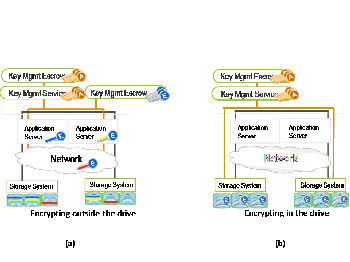
Figure 1. (a) Performing encryption outside of the storage
system increases complexity. (b) Automatic encryption in the drive
simplifieskey management for authorization (A keys) and encryption
(E keys).Source: IBM, LSI, and Seagate partnership
Click to see full imageJust the Beginning
Encryption directly on the storage device provides the simplest and most effective means to obtain a trusted storage system. An essential component of the data protection process involves key management and self-encrypting drives. Self-encrypting drives simplify the key management process. In addition, open industry specifications are the key to incorporating new technology into the data center, providing the scalability and flexibility that administrators demand.
Next week we'll provide greater detail on FDE specifications, including key management and self-encrypting drives.
- - -
Michael Willett is the co-chair of the Trusted Computing Group Storage Work Group and Seagate Research. You can reach the author at [email protected].