In-Depth
Trusted Storage for Enterprise-class Hard Disk Drives, Part 2 of 2
Full-disk encryption specifications developed by the Trusted Computing Group (TCG), including key management and self-encrypting drives, can keep data safe.
by Michael Willett
Last week (http://esj.com/Storage/article.aspx?EditorialsID=3423) we discussed the need for trusted storage and full-disk encryption (FDE) for the data center. This week we provide greater detail about FDE specifications developed by the Trusted Computing Group (TCG), including key management and self-encrypting drives (SED).
TCG Storage Specification -- The Enabler
Released to the public in June 2007, the TCG Storage Specification Overview and Core Architecture Specification, Version 1.0, Revision 0.9, was developed by TCG’s Storage Work Group (SWG). Consisting of experts from the leading storage companies, this Work Group has been working diligently on the eminent release of Revision 1.0 this year. Common use cases for storage that were taken into account in the development of the specification include enrollment, connection, protected storage, locking and encryption, logging, cryptographic services, and firmware downloads. In parallel with the core specification that covered a superset of functions, the SWG is defining selected subsets of the specification for specific applications, called Security Subsystem Classes (SSC).
To address keys in an enterprise environment, the Key Management Services Subgroup (KMSS) of TCG recently released TCG Storage Work Group Application Note 1: Encrypting Drives in an Array Controller. This document covers the historical issues and challenges in life-cycle key usage and management. For developers, the Application Note provides a detailed method and uniform approach for managing the locking and encryption of a variety of storage devices, including hard drives.
The Application Note describes secure communication and authentication between the storage device and the host by addressing the operations between the host platform, an application, and trusted storage devices. In addition to establishing compliance with existing security regulations, the specification has the flexibility to meet future state and federal legislation.
KMSS used a bottom-up approach to the secure storage hierarchy. For the data center, the bottoms-up approach avoids proprietary solutions across the whole hierarchy. Both the storage devices and the key management of storage directly on the drive - the bottom two layers - are therefore standardized, which is a benefit for end users because it simplifies the requirements and the cost for these layers by opening the sourcing possibilities to many suppliers. Storage devices with the same interface from a variety of suppliers drive competition to improve products for simplified implementation, lower cost, and easier migration.
Encrypting Outside Versus Inside the Drive
In the data center, there are many reasons to perform encryption directly on the hard drive as opposed to some point upstream. Data de-duplication and data compression as well as complexity were discussed last week. The complexity issue can provide even more compelling reasons for self-encrypting hard drives.
Encryption performed anywhere except in the drive increases system complexity. One of the more important aspects of encryption includes managing the encryption and authentication keys (or passwords). The authentication key unlocks the FDE drive. The encryption keys for the FDE drives are established in the factory by on-board random number generators. For security, the drive only stores the hash value of the authentication key for comparison during authentication. For further security, the encryption key never leaves the drive, but it is encrypted under the authentication key and stored on the drive. The encryption key is decrypted to enable operation every time the drive is unlocked. While obviously aimed at security, this process also reduces complexity in a data center.
Figure 1 shows how encrypting at the drive eliminates database administrators and application developers, as well as operating system (OS), encryption engine and network issues. Adding drives is quite simple, since each drive comes with its own encryption key and encryption engine. To add a drive, the same authentication key can be used and an automated process can handle the key assignment.
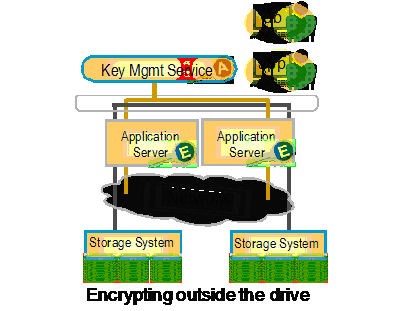
Figure 1: Database administrators (db) and application
developers (app) have less involvement in the encryption
process when it is performed in the storage device.
Encryption performed in on-drive hardware matches the drive port’s maximum speed, avoiding performance degradation common with software approaches. Since the encryption technology is on the drive, it is transparent, and scales linearly and automatically. For greater system simplicity, no changes are required in applications, databases or the OS.
Data classification is another area greatly simplified with FDE. Since encrypting more data with self-encrypting drives does not reduce system performance, there certainly is no need to make fine-grained decisions regarding what data to protect. In most cases, this could eliminate the need for data classification.
Perhaps the best example of reduced complexity is when a drive leaves the data canter. Whether a drive needs to be repurposed, returned for service, or decommissioned, a simple process provides quick and secure deletion of the encryption key, making the encrypted data inaccessible to others.
At the same time, the separate authentication and encryption keys solves the problem of losing keys and consequently losing access to encrypted data and certainly avoids the need for administrators to periodically change encryption keys.
Security Subsystem Classes (SSC)
Everything that could possibly be required for security in a storage system is defined by TCG’s Storage Work Group in the Trusted Storage core specification. To focus on specific devices, the SWG is developing a subset of functions for a PC client, servers, optical storage, and other security subsystem classes (SSC). Three SSC documents are almost complete that address laptop, the enterprise (or data center), and optical storage.
Storage security functions specific to a data center are found in the Enterprise SSC specification. Selected from the all-encompassing core specification, this profile identifies the functions that must be implemented to achieve compliance for trusted storage in an enterprise environment. Additional SSCs are in development.
For optical storage devices, SWG’s Optical Subgroup is developing an optical SSC for FDE and security functions. In the near term, other storage device SSCs are not anticipated. However, industry experts could develop an SSC for low-end storage, such as flash, by specifying the relevant security functions in those environments.
As a result of TCG’s SWG efforts, FDE will be implemented in desktop PCs, USB drives, notebooks, enterprise-class drives, tape drives that are self-encrypting, direct access storage (DAS), and network access storage (NAS). Figure 2 shows the many locations and the encryption keys as well as the central, single location for authorization key management.
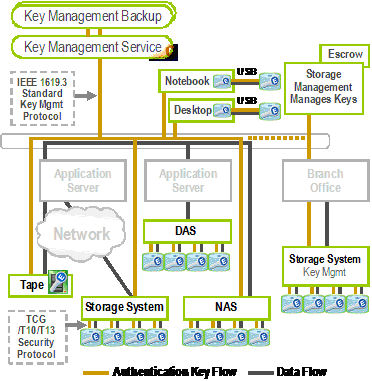
Figure 2. The goal and vision for self-encrypting storage
is protection for all data storage in the enterprise.
The Future of Self-Encrypting Storage
With its industry-developed and approved specifications, TCG has paved the way for implementing trusted storage throughout the enterprise. Compared to other encryption technologies, self-encryption within the hard drive brings significant performance, management, and security benefits to users. It also addresses issues that encryption has faced in the past.
To avoid interoperability and other issues, TCG’s Storage Work Group worked in cooperation with the IEEE P1619 Security in Storage Working Group to develop its specifications. The activities of these two organizations have minimal overlap, if any. In contrast to IEEE P1619.3 that deals with the higher-level key management protocols, TCG addresses the controller to the drive interaction. The two are compatible. The encryption algorithms are the same in either case. TCG’s standard establishes how the encryption and authentication keys are managed.
By addressing complicated issues that have made encryption a stumbling block, TCG is making encryption a “must have” part of any organization’s trusted storage strategy. With the entire storage industry behind the specification and involved in developing the various SSCs, it is fully expected that FDE will be in all aspects of data storage in the near future. Self-encrypting drives (SED) will become the accepted standard for implementing FDE. In the future, 2008 could be viewed as a major milestone in the storage industry, when security became an integral part of the storage system and protecting data in enterprise data centers became a given.
Michael Willett is the co-chair of the Trusted Computing Group Storage Work Group and Seagate Research. You can reach the author at [email protected].