In-Depth
Vulnerability Management: Assess, Prioritize, Remediate, Repeat
Results of AberdeenGroup research shed light on best practices in vulnerability management
by Derek E. Brink
Between June and July 2008, Aberdeen examined current industry practices for identifying, prioritizing, and remediating vulnerabilities to critical IT infrastructure. The experiences and intentions of more than 100 organizations from a diverse set of industries are represented in this study. Aberdeen supplemented this online survey effort with interviews with select survey respondents, gathering additional information on vulnerability management strategies, experiences, and results.
Any organization whose business operations involve networks, computers, and application software -- in other words, virtually all organizations -- is at risk for vulnerabilities in these assets that can potentially be exploited, leading to unauthorized access, exposure of sensitive data, disruption of services, or failure to comply with regulatory requirements. Vulnerabilities in computing infrastructure have many sources, including software defects, improper configurations, and simple human error.
The sheer number of threats and vulnerabilities is daunting. Industry sources cited an average of 124 new vulnerability disclosures per week for the full year of 2007, not to mention over 400,000 new examples of malicious software (including viruses, worms, back doors, key loggers, trojans, spyware, and rootkits). In addition, there is a strong trend towards exploits that are highly organized and financially motivated, upping the ante with respect to risk.
Trying to keep up with these vulnerabilities and threats is consuming a healthy percentage of the typical IT security budget -- an average of about 14 percent for all respondents in Aberdeen's recent benchmark study. No respondent interviewed felt that managing vulnerabilities was a strategic activity, yet most conceded that it was important. In general, ignoring or deferring patches for known vulnerabilities (in the absence of any other compensating controls) is not a responsible strategy, nor is it reasonable for most companies to disconnect their business from the Internet. Managing vulnerabilities simply has to be done, and the top performers in Aberdeen's study are doing it more effectively and at lower total cost.
Vulnerability Management
For the purposes of Aberdeen's study, vulnerability management (VM) refers to the process of detecting, prioritizing, and eliminating the vulnerabilities that put an organization's IT infrastructure at risk. A simplified vulnerability management lifecycle includes three basic stages:
- Assess: identify all vulnerabilities and threats relevant to the organization's IT assets
- Prioritize: determine which vulnerabilities and threats should be addressed first, based on the level of risk and the business value of the IT assets in question
- Remediate: deploy software patches, configuration updates, or compensating controls
Unfortunately, each week brings a new wave of threats and vulnerabilities to be managed, so these steps must be repeated on a regular basis -- in the limit, on a continuous basis -- to manage risk within acceptable limits. The objective of VM is to accomplish this while maximizing efficiency and minimizing total cost.
As much as one may dislike it, vulnerability management is a necessary function for any organization with business operations that involve Internet-facing networks, computers, and application software. Once we accept that VM is essential, the best results are achieved by making it as efficient and cost-effective as possible:
- Not all vulnerabilities and threats need to be identified and tracked -- just those that are relevant to the organization's IT assets
- Not all vulnerabilities and threats need to be addressed with the same degree of urgency -- prioritization should be determined based on the level of risk and the business value of the IT assets in question
- Not all remediation need to be based on deployment of software patches or configuration updates (although these processes should be automated to a much higher degree than that currently indicated by the research) -- compensating controls can also be considered in circumstances other than those in which no patches or updates are available
We must also accept that vulnerability management is a never-ending process, and that the cycle of assess, prioritize, remediate must be continuously repeated. Through better security governance (allocation of limited IT resources) and risk management (prioritization based on business value and the organization's appetite for risk), Best-in-Class performance in the "unrewarded risks" of VM will release precious IT resources an organization can invest in projects more directly tied to the "rewarded risks" of innovation and strategic growth.
Best-in-Class Vulnerability Management
A closer look at the companies in the study with top performance -- referred to by Aberdeen as "Best-in-Class" -- shows the degree to which they have developed their vulnerability management initiatives beyond those of the worst performers ("Laggards") and those in between (the "Industry Average").
Process
Interestingly, consistent policies for managing patches and vulnerabilities are not yet in place to the same degree as security policies in general. Proportionally, the Best-in-Class have given slightly higher priority to vulnerability management than their counterparts. The emotional difference gleaned from direct interviews has to do with viewing VM as an essential function to be optimized, as opposed to viewing VM as a loathsome tax on limited resources to be done as time allows.
Organization
The research indicates that organizations with top performance make strong use of external products and services for vulnerability management. In this study, the Best-in-Class spent 37 percent of their VM budget with external solution providers, compared to 25 percent by the Industry Average and just 16 percent by Laggards. This has not come at the expense of developing in-house expertise in vulnerability assessment and remediation, however, which the Best-in-Class have done to a higher degree than their counterparts.
The Best-in-Class also invest in training by a factor of more than two compared to Laggards. Investments in technologies and services that enable higher levels of automation will provide immediate access to their embedded expertise, but this does not obviate the need for training. On the contrary, increased automation of the most repetitive, complex, and time-consuming VM tasks implies a higher need for internal expertise for those few issues that will inevitably remain outside the scope of the automated solutions.
Knowledge Management
Best-in-Class organizations in the study have better visibility into the key information they need to manage across the entire vulnerability management lifecycle. An inventory of IT assets and vulnerability, patch, and configuration scans help to identify the threats and vulnerabilities that are most relevant to the organization, and to determine which vulnerabilities and threats should be addressed first based on the level of risk and the business value of the IT assets in question. A staging/testing capability helps to verify the success of software patches, configuration updates, or compensating controls in a controlled environment before widespread deployment on production systems. A database of remediations provides a valuable resource both for implementation and for subsequent audit and reporting requirements.
Technology
Across all respondents, the average level of automation for managing patches and vulnerabilities was estimated at 57 percent, with no material distinction between the three maturity classes. Increased investments in automating and simplifying the elements of the VM lifecycle represent a significant opportunity for all companies to increase operational efficiencies and reduce the total costs for this essential function. Best-in-Class organizations make more use of key enabling technologies and services for vulnerability management than their Industry Average and Laggard counterparts, including:
- Penetration testing
- Vulnerability assessment
- Intrusion detection/prevention
- Patch management
- Configuration/change management
- IT asset management
- Incident response
Across all respondents, a comparison of current deployments with planned deployments in the next 12 months indicates healthy year-over-year growth rates for these solutions, ranging between 20 percent and 50%. Emerging technologies to keep an eye on include tools that simulate (rather than scan for) threats, vulnerabilities, and exploits (see Figure 1).
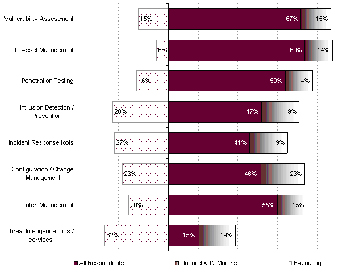
Figure 1 - Vulnerability Management Technologies
(Current / Planned / Under Evaluation)
Source: Aberdeen Group, July 2008
Click to see full image
Performance Management
In Aberdeen's research framework, performance management refers to what companies measure, and how frequently they measure it. Best-in-Class companies in this study are three times more likely than Laggards to monitor external sources for vulnerabilities, threats, and remediations, an important element in the assess stage of the vulnerability management lifecycle. In addition, the Best-in-Class are two-times more likely than Laggards to measure ROI for their vulnerability management initiatives. This is consistent with the general notion that since the vulnerability management function has to be done, it should be done as efficiently and cost effectively as possible.
Other Findings
Best-in-Class organizations in this study indicated an impressive marginal return on investment (total vulnerability-related costs avoided versus the total cost of investments in vulnerability management) of over 90%. The overall ROI, however -- total vulnerability-related costs avoided, in comparison to the total cost of investments in VM plus the total vulnerability-related costs not avoided -- was just 8%. All other respondents, however, realized a negative 8 percent per year overall return. In other words, in spite of their investments in managing threats and vulnerabilities, the majority of organizations are currently not able to keep up.
Summary
The explosive growth in the number of threats and vulnerabilities to Internet-facing networks, computers, and application software simultaneously demonstrates two things: the extreme cleverness and resourcefulness, and also the utter greed and depravity, of human nature. We can marvel at both. We should also accept both as given in our assumptions and planning relative to managing risks and allocating resources for IT security.
So long as business operations are connected to the network, vulnerability management is a necessary and essential function. Aberdeen's research confirms that the best results are achieved by making it as efficient and cost-effective as possible. By moving more of the vulnerability-related costs from the "not avoided" to the "avoided" bucket, and by automating and streamlining the elements of the VM lifecycle to minimize total costs, Best-in-Class organizations are successfully turning a necessary evil into a positive ROI.
Editor's note: A complementary copy (short registration required) of the full report is available through September 26, 2008 only here.
- - -
Derek E. Brink, CISSP is a vice president and research fellow for IT security at AberdeenGroup, a Harte-Hanks company. You can reach the author at [email protected]