In-Depth
Getting the NAC of Network Access Control
Network access control is a hot topic, and there’s more clarity than marketing hype about the technology. We look at the basics of NAC and where it’s headed.
Network Access Control (NAC) is one of the hottest topics in network security these days. Every vendor seems to be coming out with a "NAC solution" with the same promise—it will clean up your network and solve all your security problems. Fortunately, NAC technology has matured to the point where clarity is beginning to emerge from the marketing hype. We can now identify the true value of NAC in the enterprise, objectively evaluate the pros and cons of different approaches, and make more informed NAC deployment decisions.
Several converging trends are pushing businesses to adopt NAC. First, networks are more open and therefore more vulnerable than ever:
- Wireless networking and remote access have extended the corporate network to many homes, hotels, and coffee shops around the world. Providing greater network access to partners and contractors improves business efficiency, but further opens the network to uncontrolled devices.
- Laptops and other mobile computing devices that may carry sensitive corporate data are widespread and constantly exposed to Internet threats. These devices need stronger protection and monitoring.
- Regulations and public pressure to protect sensitive information now require enterprises to establish and maintain tight controls on networks and endpoints.
What is NAC? The main concept is that IT needs to control network access based on factors such as user identity, machine health and identity, time of day, and other factors. Like most IT solutions, NAC is not really new. From timesharing to modem pools to virtual private networks, we have always controlled access to computing resources based on user identity. What's new with NAC is that we're moving beyond user-based access control to include an examination of the device used to gain access to the network—and we're extending access control to every part of the network. By including device health and identity in network access control, all endpoints (network-connected devices) can be identified, managed, and kept healthy.

Figure 1: The NAC Process
To understand NAC more fully, we must understand the three-step process of NAC, as illustrated in Figure 1:
- Assessment: user identity and endpoint health are established
- Enforcement: granting or limiting network access based on policy
- Remediation: fixing problems with the endpoint as necessary
After remediation, the cycle resumes with assessment. Good NAC solutions provide constant reassessment (since new threats are always emerging). They also provide strong management tools to monitor compliance, debug problems, and establish access policies (who can do what when) and endpoint health policies (what's allowed on endpoints).
There are two primary approaches to NAC, as illustrated in Figure 2.
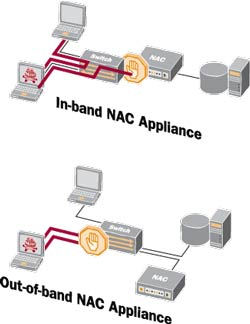
Figure 2: NAC Approaches
In-band NAC appliances are inserted at critical points in the network. They combine assessment, enforcement, and remediation in one box, simplifying deployment. On the down side, they provide limited enforcement (only restricting traffic that passes through them), are expensive (since they must operate at wire speed) and sometimes require separate user authentication.
Out-of-band NAC appliances integrate with switches, routers, and other networking gear (DHCP servers, VPN gateways, wireless access points, firewalls, etc.). When a new endpoint connects, the networking gear informs the out-of-band NAC appliance which performs assessment and remediation. If enforcement is required, the NAC appliance notifies the networking gear, which restricts or grants access as needed. An out-of-band NAC solution is generally much less expensive than an in-band NAC solution because a single appliance can manage an entire network. Out-of-band NAC can also be more secure since it can perform enforcement at the edge of the network, stopping unhealthy machines before they can infect anyone. Out-of-band NAC is more complex because it requires integrating the NAC appliance with the networking gear.
Assessment varies among NAC solutions. Some use pre-installed agent software on the endpoint, some download agents through a browser. Still others perform an external scan or simply monitor network behavior. Less intrusive problem detection assessments are generally less effective. The ultimate in secure assessment is to use the Trusted Platform Module (TPM), which is included on all recent laptops. This chip can detect root kits, which are otherwise almost undetectable. Today _ s NAC solutions often combine several assessment modes for maximum flexibility.
After examining the range of NAC solutions, one theme emerges: multi-vendor integration. A NAC system involves several components: endpoints, networking gear, and NAC appliances. These components (especially endpoints) often come from several vendors. Assessment often requires integration with client security software (such as anti-virus and patch management).
The need for multi-vendor integration in NAC systems has led to the emergence of several NAC architectures with well-defined integration interfaces such as Cisco's Network Admission Control (C-NAC, sometimes given the confusing acronym NAC!), Microsoft's Network Access Protection (NAP), and the Trusted Computing Group _ s Trusted Network Connect (TNC). While these architectures are similar, one key difference is that C-NAC only works with Cisco networking gear and NAP only works with the Microsoft Windows operating system. In fact, they only work with the latest versions of these products. TNC, on the other hand, is an open-standard architecture. The TNC specifications (along with white papers and other support documents) are available on the TCG Web site (see https://www.trustedcomputinggroup.org).
The trend toward consolidation and open standards in the NAC arena will certainly continue, as it has in the rest of the networking world with TCP/IP, HTTP, SMTP, and others. Given the essential nature of multi-vendor integration for NAC, it will probably be even more rapid for NAC than for e-mail and other networking protocols. The move towards open NAC standards should ease NAC deployment and reduce costs, certainly a welcome development for networking and security architects.
Steve Hanna is distinguished engineer at Juniper Networks; you can reach the author at [email protected]