
Technical and financing agreements are latest in competition among Hortonworks, Cloudera and MapR.

Big Switch Networks Inc. flagship product provides hyperscale networking technologies.

The Talend Big Data Sandbox promises "zero to Big Data without coding in under 10 minutes."

Companies emphasize bringing Big Data analytics to iPhone and iPad users.

Vendors scramble to help enterprises move their Big Data analytics to the cloud in an exploding market.
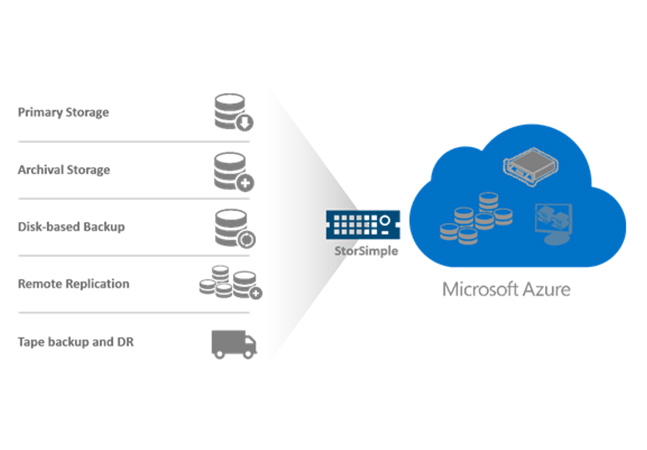
Microsoft announced this week a new line of its StorSimple appliances that link on-premises datacenters to the Azure cloud.
With a smaller piece of the market pie for everyone, consequences for Cisco are "particularly dire."

Complicated pricing, hidden costs and performance problems are main culprits.

Research shows VMware, Amazon AWS lead in private, public arenas.
Tool helps configure, deploy, run and manage virtualized Hadoop clusters.
Salesforce Wear Developer Pack provides sample apps for glasses, wristbands, smartwatches and more.

Containers are a lightweight means to develop, ship and run distributed applications on different platforms.

It's a next-generation "catalyst for enterprise innovation."

Survey shows IT and security pros wary of potentially expensive cloud data breaches.

Here is what you can do to boost both the performance and amount of storage available in your enterprise.

X-as-a-service offerings include counter fraud, digital commerce, mobile, analytics and more.

It features speedier queries, improved query-dependent allocation of resources and better SQL-on-Hadoop functionality.

The company targets services providers looking to automate their infrastructures and save money.

Cloud-based marketplace service also offers social collaboration.

While Fibre Channel provides enterprises with high-speed transfer rates, is the amount it offers a bit overkill?